How much did Garmin secretly pay to criminals who hacked into its online systems?
Reportedly Garmin paid US$10 million in bitcoin (very quickly) in apparent defiance of sanctions against doing business with cyber criminals. The same criminals who are demanding ransom money from hospitals during a pandemic.
Garmin, the makers of popular GPS watches and devices that link to Strava and other online communities was attacked by sophisticated online criminals and paid them off to regain control of customer data.
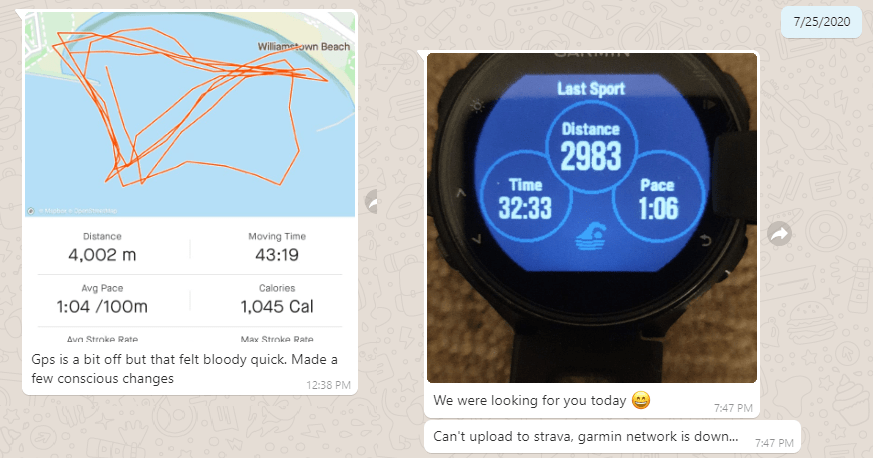
You may have found that the Garmin network has been having problems recently. You might not have been able to upload your run or swim to Strava.
Garmin was attacked on 23 July. The criminals used the WastedLocker ransomware developed by Russian based Evil Corp. Yes that is its real name.
The US government has placed sanctions on Evil Corp and companies that do business with Evil Corp or criminals using WastedLocker and other Evil Corp products like Dridex.
Garmin tried to pay off the criminals very quickly, to get their systems back up and running, but that didn’t work because the intermediary company backed out, fearing the US sanctions.
But Garmin successfully managed to pay off the criminals, using another intermediary on 24 or 25 July 2020, reported IT media outlets last weekend. The criminals then provided a WastedLocker decryption key to Garmin.
Last Monday, 27 July, Garmin announced that it “was the victim of a cyber attack that encrypted some of our systems on July 23, 2020.”
“Many of our online services were interrupted including website functions, customer support, customer facing applications, and company communications,” said the company statement from Garmin.
“We immediately began to assess the nature of the attack and started remediation. We have no indication that any customer data, including payment information from Garmin Pay™, was accessed, lost or stolen.”
What Garmin didn’t say is that just one or two days after the 23 July, they had paid US$10 million in encrypted bitcoin (reportedly) to the criminals.
“Affected systems are being restored and we expect to return to normal operation over the next few days. We do not expect any material impact to our operations or financial results because of this outage.”
Can a company do business with criminals who kidnap our data?
This is said to be happening increasingly in Australia. A surge in ransomware attacks on companies and customer databases in 2020 was reported last week by the Office of the Australian Information Commissioner (OIAC).
Online security company MacAfee reported that NetWalker ransomware business is booming – A$35 million in extorted Bitcoin from companies globally in the last four months.
Some of that money has come from Garmin (customers) and apparently now NetWalker is being upgraded.
The original version used emailed messages to unlock machines but now a “security code” must be entered into a darkweb website. NetWalker now offers criminals “instant and fully automatic payments” according to advertisements on the dark web.
One IT media outlet asked the criminals behind NetWalker if they would stop attacking hospitals during the COVID-19 pandemic.
The OIAC says health providers are the leading target of malicious attackers and the number one source of data breaches in Australia.
The NetWalker criminals responded:
“Hospitals and medical facilities? do you think someone has a goal to attack hospitals? we don’t have that goal -it never was. it coincidence. no one will purposefully hack into the hospital.”
But what if NetWalker has been deployed into a health service computer system already? Perhaps by accident?
The criminals were asked directly: “Will you give hospitals the decryption code for free?” (you know, so they can get back to saving lives … ) and they replied, directly:
“If someone is encrypted, then he must pay for the decryption.”
More on the recent OIAC report at my blog.